The method i am about to show you will become somewhat useless in the future. I will show you WHY. Everyday more and more people are switching over to WPA and WPA2 for wireless security. More and more router manufacturers are setting WPA as the default security standard of their routers. I would love to go into the history of wireless security, but i want to keep this post short and to the point. all you have to know is that WPA is definitely MORE SECURE than WEP.
As this is a public blog, i shall emphasize that i am posting this for educational purposes only.
You have to understand that i try to be as ethical as possible with the knowledge i've acquired over the years.
"What is ethical about showing people this information?" you might ask.
I gathered my knowledge from multiple free and open sources on the internet. Information should be free and open to anyone. YOU have the same right to it as I do and YOU make the choice on what to do with it.
This is my own personal belief, plain and simple.
The laws regarding unauthorized access to wifi networks varies from state to state
I am posting the following link as a WARNING to those who may have abusive/ill intent:
http://www.ncsl.org/IssuesResearch/TelecommunicationsInformationTechnology/ComputerHackingandUnauthorizedAccessLaws/tabid/13494/Default.aspx
it's not my place to choose between right and wrong for you
Moving on...
(If some descriptions seem Vague to you, i purposely mean to have it that way. If you really care, you'll do some research on your own)
WHAT YOU WILL NEED:
- A DESKTOP COMPUTER OR LAPTOP
herp derp on this right? I know you are not idiots, but we only know about idiots cause they exist, and we have all met at least one.......lets leave it a that.
- A PROPER WIRELESS ADAPTER
In this particular procedure I will be working with a NETGEAR WG111v2 wireless adapter. This is probably the trickiest part, believe it or not, mainly because you have to find it and probably spend some money on it. There are many wireless adapters out there from many manufacturers. What makes this Netgear adapter so special Manni? The firmware inside of it.
Again to keep this short, you can find lists of adapters which have a firmware suitable for WEP and WPA cracking online.
- BACKTRACK 3 (LINUX)
YES, you read Linux.........does this intimidate you? don't let it. Backtrack is an operating system which can be run from a Linux "Live-CD." This means you can load the CD into your CD-ROM drive and restart your computer. The Live-CD loads automatically with Linux on your computer. most of yours will say something like "press any key to boot from CD" or something similar. The neat thing about live CD's is that you can take out the Live-CD and restart your computer and Windows/OSx (yup they are Mac friendly) will load up as if nothing ever happened. They are completely safe to use.
For the purposes of my own procedure I run a program called VMware which lets me simulate a virtual computer on my desktop. Naturally i loaded the BACKTRACK3.ISO file.
THE HACK:
I have read multiple guides out there on how to do this and most ALL use a program called Aircrack-ng. They involve inputting command lines to achieve the feat I am going to perform, BUT to make it easy on YOU, it will be based on programs that have a Graphical User Interface. What does this mean Manni? it means pretty pictures! NO COMMAND LINES!
-Step one
Make sure Backtrack 3 detected the Wireless adapter. The easiest way to check for this is to open the "Wireless Assistant" from the Backtrack 3 Start menu.
start >> Internet >> Wireless Assistant
When the program opens it will say "Initializing" at the bottom. If you have a proper wireless adapter it will begin displaying wireless networks for you to connect to. If you see wireless connections on the list it means the adapter is working. go ahead and close the program.
-Step Two
We are now ready to Sniff out wireless networks. How is this different than just using the Wireless Assistant to find wireless networks? A Sniffer will not only go out and find wireless networks, It will give you other variables specific to the wireless network such as the MAC Address, BSSID, Channel, and Packet Count...etc.
The Sniffer program we will use is called KISMET. I'll be honest KISMET is not technically a Sniffer but i use this term because i relate it to looking for specific information which may be useful. There are programs that have better functionality than KISMET, but it's what i feel comfortable using.
to open KISMET in BACKTRACK 3:
Start >> Backtrack >> Radio Network Analysis >> 80211 >> Analyser >> Kismet
You will get the following window:
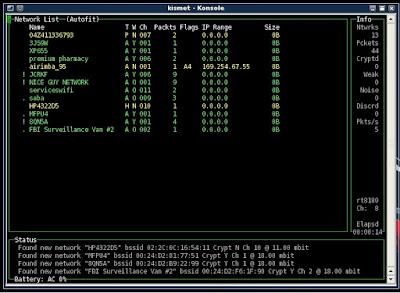
What we want at this point is to sort the networks by "PACKET COUNT"
you can achieve this by pressing the letter "S" to open the sort menu, Then press "P" to sort by packet count. You want to find a WEP secured network with the highest packet count. You have to understand that Signal strength DOES NOT always mean high packet count.
In Kismet the networks with the highest packet count will go to the bottom of the list and that is where we want to start after sorting:
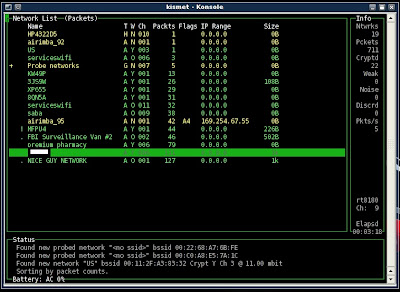
Scroll down with the arrows on your keyboard and hit enter on a network. DISREGARD THE NETWORK NAME for the moment. The goal is to find a network that is WEP secured. We select and press "enter" on a network and press "Q" to return back to the list of networks
so what are we looking for manni?
what you need from this window are 3 things
"Encrypt : WEP"--tells us this is in fact a WEP secured network
"BSSID : 00:24:D2:B9:25:22" -- Tells us the BSSID which is the network's MAC address
"Channel : 6" -- tells us the CHANNEL number of the network. this number will always be between 1 and 11
***WRITE THIS INFORMATION DOWN. YOU WILL NEED IT***
This is what it looks like:
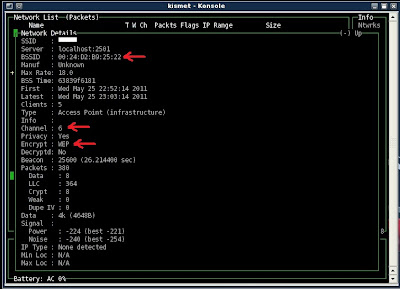
you may now close Kismet and proceed...
-Step Three
At this point we have found the network we want to access, you may have noticed I whited-out the actual name of the network for my own protection. though you can still see the BSSID and the CHANNEL number.
really that's all you need when cracking WEP security.
we will now open a program called SpoonWep.
Start >> Backtrack >> Radio Network Analysis >> 80211 >> Cracking >> SPoonWep
You will notice immediately why i love this program.
All we have to do now is input the information we gathered from kismet.
In "Victim Mac" we simply input the BSSID
In the "NET CARD" drop-down you select your wireless adapter. In most cases it is called "Wlan0"
Then, we slide the channel selector to the proper channel gathered from Kismet
***DISREGARD ALL OTHER VARIABLES***
Yeah, i could definitely explain what they mean but for the purposes of learning a simple hack they will be irrelevant to you. Though, I will point out the name of the hack. It is called an "ARP REPLAY ATTACK"
It will look like this:
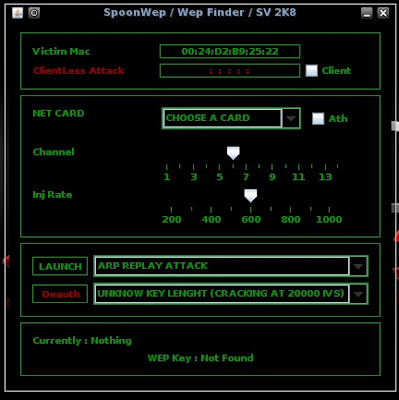
We want to subsequently "LAUNCH" the attack.
A window called "WS DUMP" will appear
It will have a variable called "#Data" that increases in number when you are running the attack.
These are called IV's and they are the information used to defeat the WEP algorithm. Depending on how far away the network is this process will vary in time. Most new computers can do it in around 1 - 5 minutes. Sometimes the #data count will go very slow and it may take up to 10 - 15, even 20 minutes. BE PATIENT.
you notice on the background we also have SpoonWep counting IV's and giving you a status of "CRACKING WEP"
Here's what that looks like:
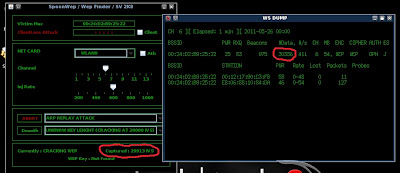
SpoonWep begins cracking the WEP key once is reaches the 20,000 mark, but the more IV's you gather the faster it will finish the attack. Again let me reiterate, if the IV count is going slow just BE PATIENT. As long as it is going up to 20,000 and above, the program WILL eventually decrypt the WEP key for you.
If all goes as I've explained then you will get:
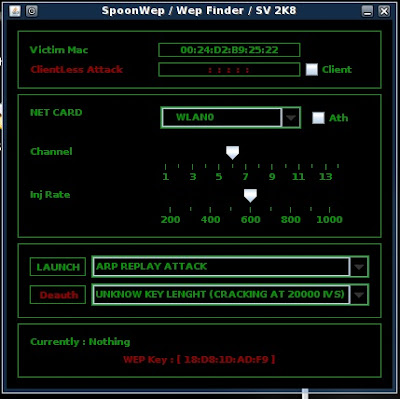
As you can see SpoonWep is displaying the WEP key for the network we found in Kismet
SpoonWep displays it separated by colons, but just disregard those. All 40-bit wep keys are exactly 10 characters long and 128-bit keys are 26 charaters long.
we just cracked a 40-bit WEP key.
And now we are DONE! YAAAY!!!
We never once opened the command line interface during this hack
not only that, It was extremely EASY.
And THIS my friends is WHY we see the standard changing from WEP to WPA/WPA2.
I hope i was able to teach you something interesting.
Have a great rest of your day/night.
Funny thing was, I actually already knew how to do this. WEP cracking is piss easy.
ReplyDeletewell in light of this information i am switching over my wireless security settings right now
ReplyDeletegreat decision Grant!
ReplyDeleteThat was helpful. I heard how WPA is better than WPE, but didn't know how to switch. Thanks!
ReplyDeleteI knew a basic idea of all this, but it's been a while since I've been out of reglancing at this, I mean it does have a few more detailed points than what I originally remember, so congrats on that.
ReplyDeleteAlso to Zoidbery, yeah WPA is better, but you switch by going to your router/modem and go to your settings. :P
Wow what a post! I've always wondered how you do this.
ReplyDeleteHoly crap! Thanks for the post. I might need this
ReplyDeleteVery informative. I'm glad I switched to WPA.
ReplyDelete@MrGbounds Thanks for the tip :)
ReplyDeleteWow i always wanted to learn this, but looks very complicated
ReplyDeleteNice tips, will do.
ReplyDeleteThanks for the tutorial. Nicely done
ReplyDeleteI have got this down to a science when I am out and about. Nice post.
ReplyDeleteNice. But nobody will ever try to hack into my router - we named it FBI Surveillance Van.
ReplyDeleteHoly smokes batman, I never thought it was possible. I just switched to WPA and am now shitting bricks.
ReplyDeleteSo I can steal my neighbor's Internet with this method? Haha.
ReplyDeleteI tried doing this when my roommate had the hotspot in his room, couldn't get it to work
ReplyDeleteYou can still find many WEP hotspots where I live. People never learn.
ReplyDeleteVery tasty colors mmmm
ReplyDeleteDoesn't having an airport capable card help speed this up?
ReplyDelete@parsnip....
ReplyDeleteairport capable?
Wow this is detailed - will have to read through again before I figure this out.
ReplyDeleteGreat info dude, damn this is detailed
ReplyDeleteNice step by step tut. Making it easy for all the normal peeps to get hackin lol
ReplyDeleteFollowing!